

















 {% endhint %}
### Claims
{% hint style="warning" %}
If you are using **SSO V2**, an additional step is required. The **claims** on the Entra side **must be entered manually** and should preferably be of type **ID**.
{% endhint %}
* In the **Token configuration** tab
* Click on **Add an optional claim**
* Add the 4 claims below:
{% endhint %}
### Claims
{% hint style="warning" %}
If you are using **SSO V2**, an additional step is required. The **claims** on the Entra side **must be entered manually** and should preferably be of type **ID**.
{% endhint %}
* In the **Token configuration** tab
* Click on **Add an optional claim**
* Add the 4 claims below:











Application information

Audience settings
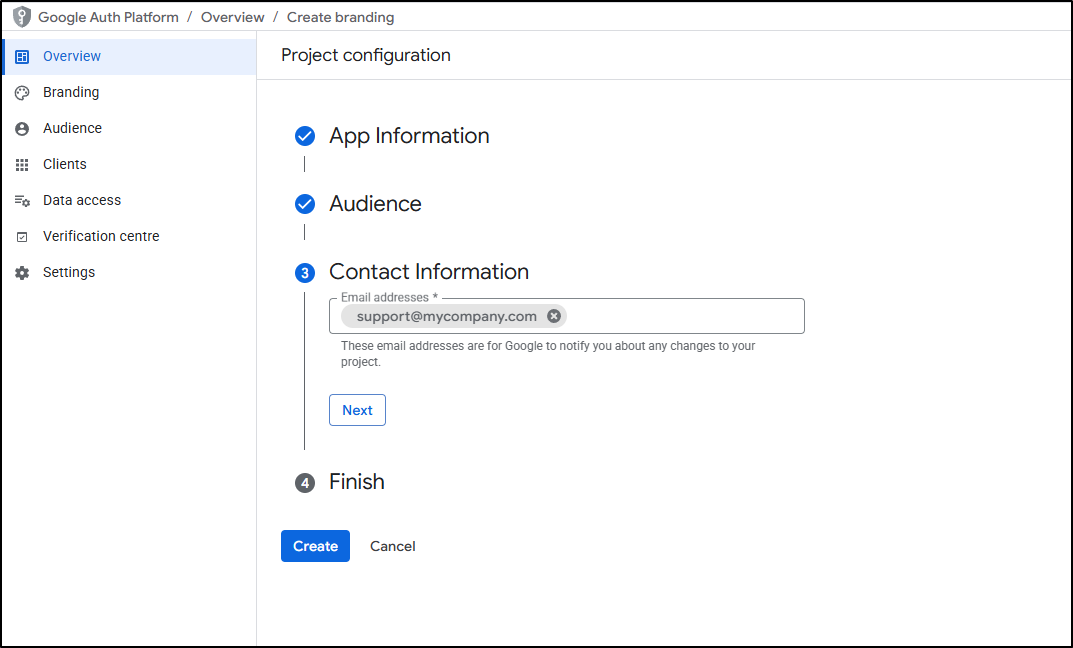
Application contact

Application finalization

Added the web application

Application creation

Retrieving the callback URL

Authorized URIs
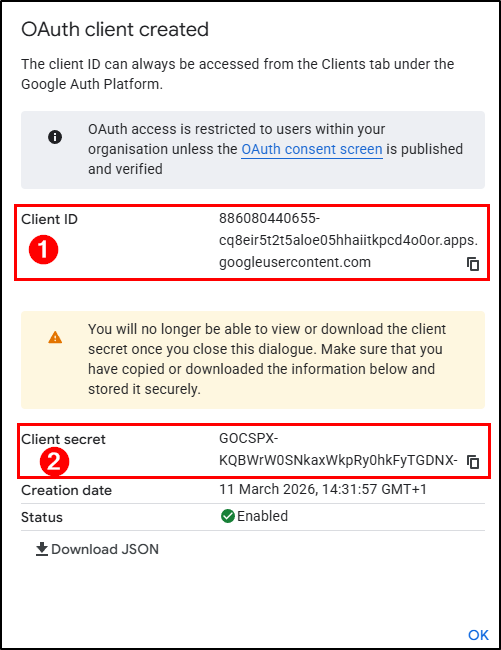
Application ID and secret

ID and application secret from GLPI

Scopes adding

GLPI homepage with OAuth SSO





























